About this course
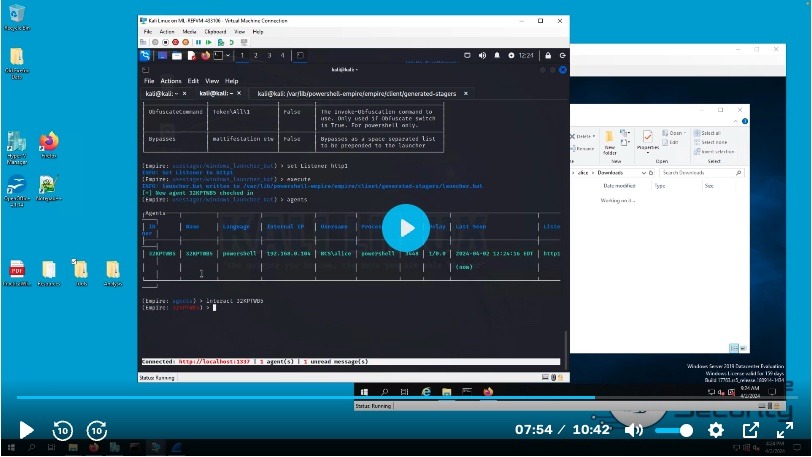
In this course, you will experience and explore a realistic cyber attack scenario. You will utilize the Empire Command and Control (C2) framework to carry out an attack on a Windows target VM. Following this, you will transition from the role of attacker to defender, conducting initial event analysis with Splunk, remote analysis and data collection with Velociraptor, and forensic analysis of registry keys and decoding obfuscated payloads. This course offers a true “purple team” approach, where you can learn from both the perspective of a red team operator and a blue team investigator.
Course Previews
Requirements
- This course builds on a lab setup, which is documented in our free Build Your Lab series.
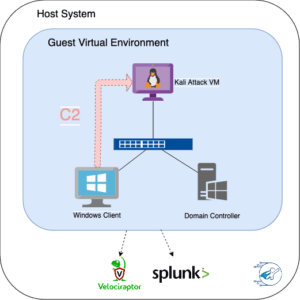
- It requires at least one Windows VM and a Kali Linux VM.
- Additionally, you will need a host VM with the following tools installed.
- Splunk
- Velociraptor
- Forensic tools
Lab Architecture
Instructions on how to set up the lab environment are provided in the course.
Support & FAQs
Reach out to us and join our Discord community for general conversation topics and networking.
Certificate of Completion
Once you finish the course you will receive your Certificate of Completion! 
You must log in and have started this course to submit a review.