Investigation and Analysis
How to analyze and investigate compromised systems.
What’s the best way to start learning or enhance your skills in digital forensics and incident response?
Digital forensics is a skill that supports the incident response process. Therefore, it is critical to possess foundational knowledge about digital forensics before stepping into incident response scenarios.
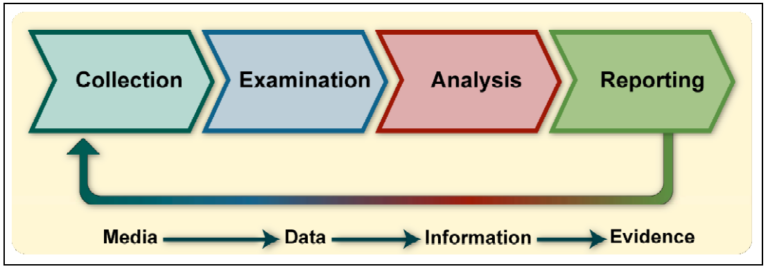
In the previous tutorials you have learned how you can set up your own forensic system, how to create a target (“victim”) and now you are ready to analyze it. When it comes to digital forensics, there are several steps that are critical to follow. As outline by the NIST SP 800-86 “Guide to Integrating Forensic Techniques into Incident Response” these steps are as follows:
Collection
What data is available and pertinent to the case? This may include logs, network telemetry, memory, and disk images of various systems. Where and how can we collect data that helps us to meet our objectives based on priority and amount of effort required? Furthermore, understanding how to safely handle the evidence based on the order of volatility is one of the most critical steps as any mistakes might lead to corruption or loss of data. Once an acquisition plan is executed and the collection has finished, especially in real-world scenarios it is highly recommended to create hash sums of the data to ensure the integrity of the data is preserved in subsequent steps.
Examination
Once the data is collected, you need to assess and extract the pieces of information that are relevant for further forensic analysis. This may involve using commercial forensic suits. However, many freely available tools as described in building your forensic workstation are being used by professionals to extract and examine various sources of information.
Analysis
The analysis requires a clear methodological approach to reach appropriate conclusions. This may include correlating data across different sources. It is critical that as a DFIR professional you are intimately familiar with forensic artifacts, are properly trained, and possess the skills to effectively analyze and interpret the data.
Reporting
Depending on the objectives of the case the type of reporting may vary. It typically requires presenting final conclusions and explanations regarding an event. However, during incidents, time may be of the essence and the objectives may be to quickly identify indicators of compromise, potentially stolen data, lateral movement, etc. to understand attacker behavior and to further the investigation.
How to proceed from here..
Curious about learning hands-on technical skills that matter from industry experts? Check out our online courses and training options!
Subscribe to our Newsletter
Stay tuned and subscribe to get updates and early access on new content!
We do not sell any data. You can unsubscribe easily at any time!