By Markus Schober, Founder of Blue Cape Security
One of the most common frustrations I hear from organizations is:
“Do more with less,” or “We’ve invested in X number of tools, but our analysts are still struggling.”
This post was born from years of seeing that disconnect up close. I’ve worked with security operations centers (SOCs) across industries—from small startups to global enterprises—and the pattern is always the same: too much focus on technology, not enough on the humans behind it.
The Real Problem: Tool-First Thinking and Its Human Cost
Budgets often skew heavily toward shiny new platforms (often “point solutions”), while the people expected to operate them receive little training or context.
This imbalance leads to a few predictable outcomes:
- Underutilized technology. Tools sit idle or are used at only a fraction of their potential—often adding complexity rather than clarity.
- Alert fatigue. Analysts drown in data but lack the context to prioritize what matters.
- Burnout and turnover. When work feels repetitive or reactive, people leave.
Meanwhile, complexity keeps growing—more data, more telemetry, more systems to normalize, analyze, and act upon. Even with the promise of automation, AI, and machine learning, there will always need to be a human in the loop—someone capable of understanding, maintaining, and improving SecOps processes.
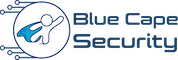
Future of the SOC: softwareanalyst.substack.com/p/revolutionizing-secuity-operations
The Human Cost
These challenges—combined with under-resourced and under-skilled teams—can have serious consequences for both people and the organization’s overall security posture.
According to the Voice of the SOC Analyst:
- 71% of analysts experience some level of burnout.
- 64% spend more than half their time on tedious manual work.
- 64% say they’re likely to switch jobs within the next year.
- 66% believe half or more of their current tasks could be automated today.
This ultimately leads to talent drain, high turnover, and low morale.
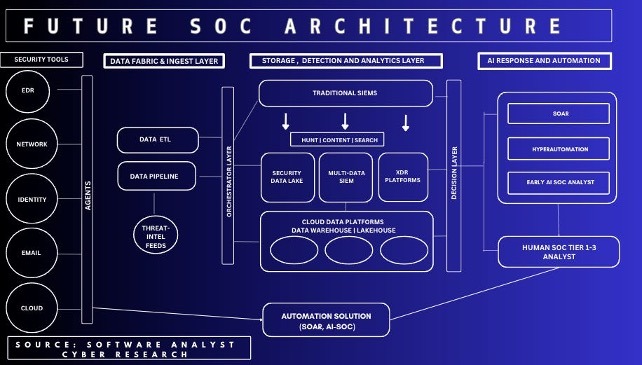
People, Process, and Technology — In That Order
It’s easy to talk about “balancing” people, process, and technology—but in reality, people are the driving force behind the other two. Tools don’t adapt on their own, and processes don’t improve by themselves; it’s humans who design, refine, and evolve both.
People – Process – Technology Trifecta
When we focus on developing people first, everything else follows. A well-trained analyst doesn’t just execute a process—they question it, improve it, and teach others. They don’t just use tools—they operationalize them, identify gaps, and find creative ways to close them.
That’s why investing in people is the single most effective way to advance process and technology together.
Lessons from the Field
Devastating Cyber Attacks
We’ve seen this play out time and again—in both government and private-sector incidents.
A recent example is the CISA AA25-266A advisory, where attackers gained access to a U.S. federal agency network and remained undetected for nearly three weeks. The case perfectly illustrates that technology alone isn’t enough—it’s the people and processes behind it that determine the outcome.
CISA’s report highlighted three critical lessons every organization should take to heart:
-
Vulnerability and patch management.
Known vulnerabilities were not remediated in time. Even though patching might sound routine, it’s ultimately driven by people—by prioritization, communication, and consistent follow-through.
-
Incident response readiness and escalation.
The agency hadn’t tested its response plan and struggled to involve third parties or provide them adequate access. This showed a breakdown in both preparation and process ownership.
-
Monitoring and alert handling.
Several EDR alerts were missed or ignored, and some systems lacked endpoint protection entirely. The technology existed, but the alerts weren’t acted upon quickly enough.
These failures rarely come down to inadequate tools—they stem from gaps in people, process, and practice: a lack of resources, skills, and structured opportunities to exercise and refine those capabilities over time.
Beyond the technical failures, we also see organizational habits that weaken the very foundation of capability—how teams train and learn.
Cybersecurity Training Became a Commodity
Over the years, we’ve also seen a concerning shift in how cybersecurity training is delivered and perceived. In many ways, it has become a commodity—and the symptoms are easy to spot:
- Theory over practice — too much focus on concepts, not enough hands-on work.
- Tools over skills — training tied to vendors rather than investigative techniques.
- Random topics — disconnected sessions with no clear development path.
- Certificates over competence — chasing badges instead of building expertise.
- Training fatigue — analysts overloaded with content but little retention.
- High cost, low impact — programs that sound impressive but fail to deliver measurable improvement (or low cost with equally low impact).
The result is a workforce saturated with information but lacking the confidence and context to apply it effectively.
The most important part of any cybersecurity training isn’t what happens during the course—it’s what happens after. Can the newly learned knowledge be operationalized? Are teams implementing new workflows, reinforcing skills through practice, and adapting methodologies based on what they’ve learned?
These lessons became the foundation for how we help teams transform their operations in practice.
Case Study: From Button-Pushers to Advanced Capabilities
One of the most rewarding transformations we’ve witnessed came from a client whose SOC team began in what I’d call the “button-pusher” phase.
At that early stage, analysts were responding to alerts mechanically—acknowledging notifications, escalating cases, and following playbooks without deeper context or ownership. Some tools and data were in place, but critical thinking, confidence, and morale were lacking.
That’s where our collaboration began. Together, we set clear goals and defined a structured path for measurable growth through three maturity stages:
-
Crawl – Building Foundations
Developing core investigative skills, strengthening understanding of artifacts and evidence, and building confidence through structured live training.
-
Walk – Applying, Operationalizing, and Expanding Skills and Tools
Translating learning into daily operations, improving workflows, and empowering analysts to use tools creatively while refining processes and collaboration.
-
Run – Specialization and Advanced Capability
Enabling team members to pursue specialized roles—ranging from threat hunting and purple teaming to operationalizing threat intelligence and running advanced adversary simulations in the Blue Cape Security Cyber Range.
What began as a reactive SOC evolved into an engaged, motivated, and technically proficient team. Each analyst developed their own specialization, contributed to process and tooling improvements, and took pride in continuous learning. The result was a culture of ownership, curiosity, and confidence—where people no longer just pushed buttons but built lasting capability through an ongoing cycle of learning, practice, and validation.
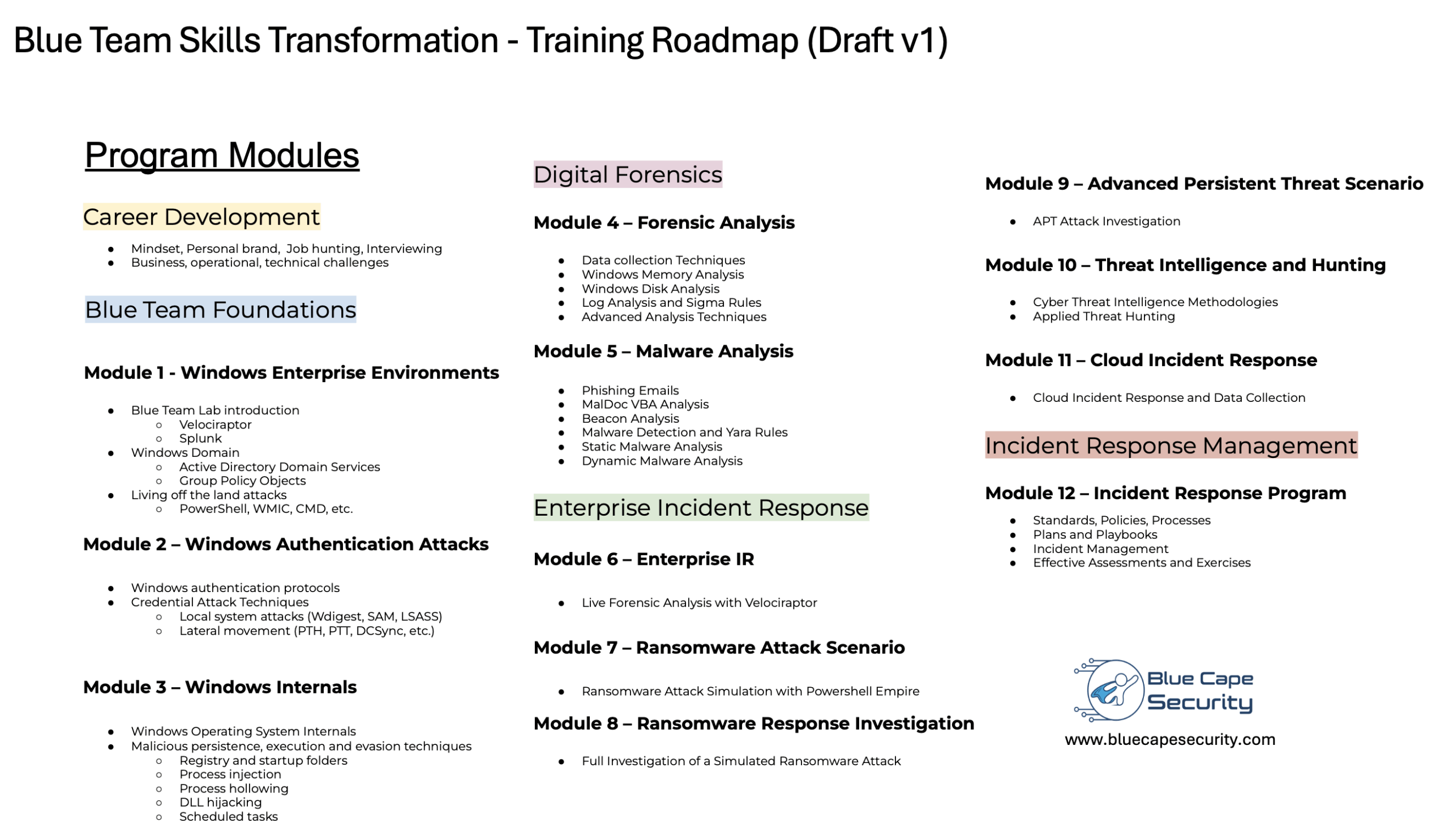
Blue Cape Security – Training Roadmap draft
The training roadmap we developed and followed for this client is shown below. It became the foundation for what has since evolved into our current on-demand training catalog—covering the full journey from 101 Enterprise Fundamentals to 200 Forensic Analysis and the advanced 300 DFIR Training Tracks.
Results That Last
The outcome wasn’t just improved incident handling—it was a complete mindset shift.
Team members began leading initiatives, mentoring newcomers, and driving process and tooling improvements on their own. What used to be a reactive team became a proactive force for innovation and growth.
By investing in structured education, hands-on practice, and continuous validation, the organization built something no tool or platform could deliver: a culture of curiosity, ownership, and resilience—one that naturally drives stronger tool adoption and sustained operational excellence.
Building Sustainable Capability + Maturity Framework
You can’t buy capability—you have to build it. That starts with a clear, measurable plan that connects education, practice, and process. Here’s our framework for building a capable, consistent, and continuously improving security team:
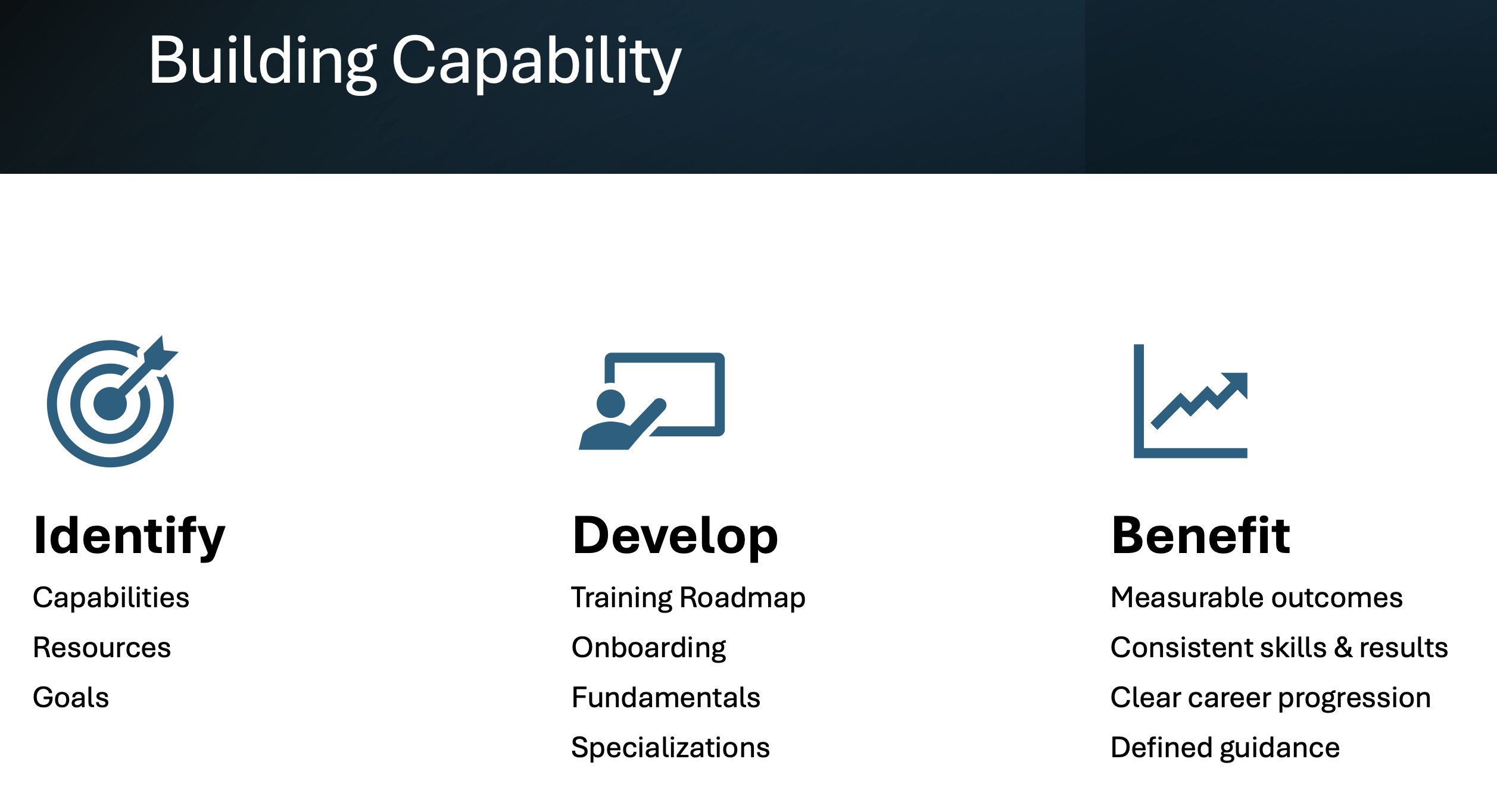
Building a Training Roadmap
Building true capability starts with understanding where your team stands today. That means identifying existing skills, resources, and goals—what’s working, what’s missing, and where you want to be in the next few months.
Once that foundation is clear, the next step is to develop a structured roadmap that aligns with your organization’s priorities. This includes strong onboarding for new analysts, reinforcement of fundamental skills, and guided pathways into specializations—all mapped across 3-, 6-, and 12-month milestones to measure progress and sustain motivation.
The real impact comes from what follows: the benefit. Leaders gain measurable insights into their team’s growth, consistency in performance, and confidence in having people who know where they’re headed. With a clear career development plan and defined guidance, both individuals and organizations grow together—steadily and sustainably.
The Blue Cape Security Training Maturity Model
After guiding multiple organizations through this transformation, we began to recognize a consistent pattern—recurring challenges at each stage and clear objectives that defined progress. This insight led us to formalize the Blue Cape Security Training Maturity Model, a structured framework for developing people, processes, and capabilities over time.
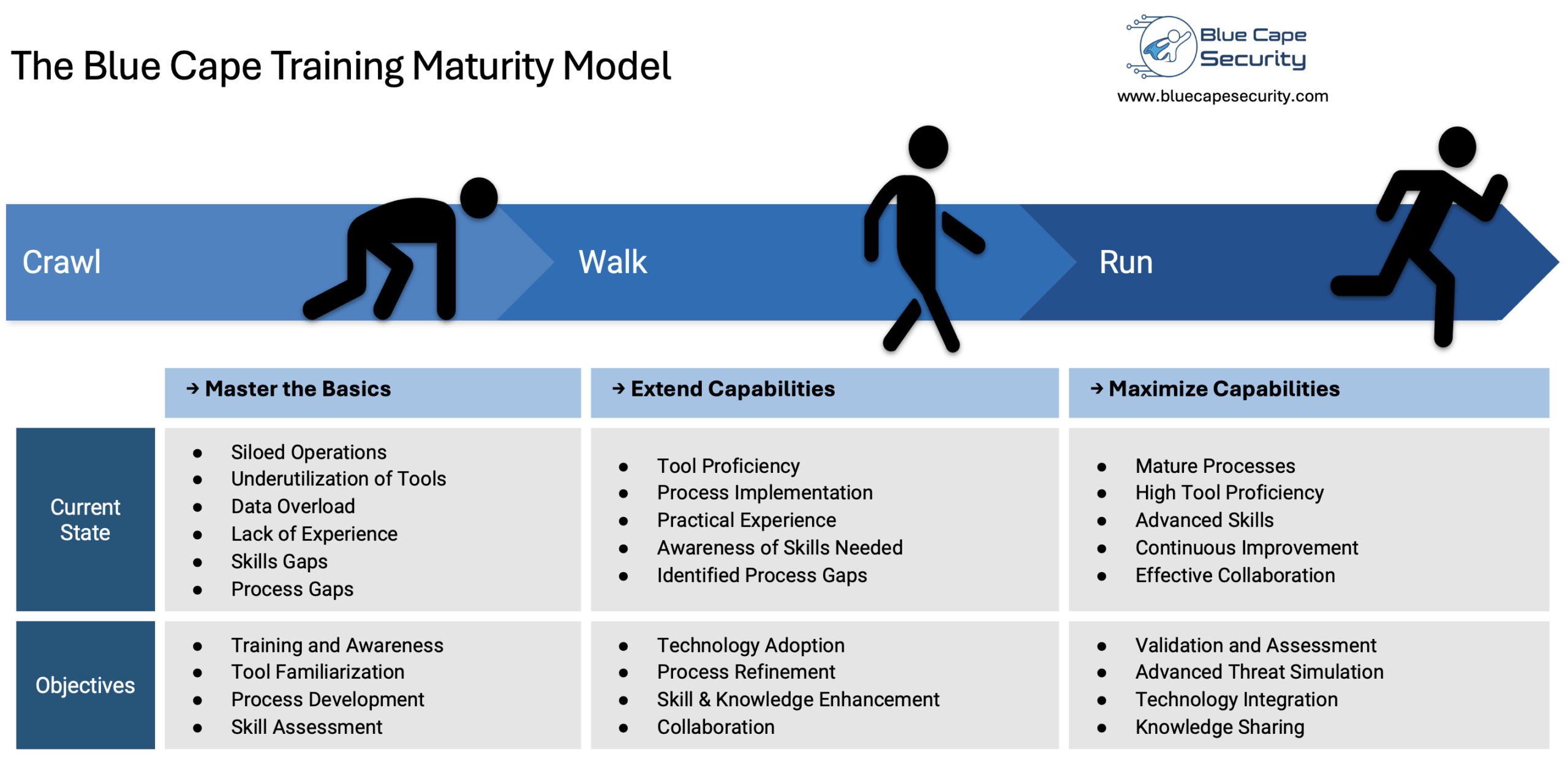
The Blue Cape Security Training Maturity Model
Key Takeaways
To truly strengthen your cybersecurity posture:
- Invest in people and skills first.
- Establish clear development paths and milestones.
- Create an effective onboarding and continuous learning process.
- Use offense-informed defense to stay adaptable.
- Maximize your existing technology before buying more.
Threats will continue to evolve.
Your best defense is a motivated, skilled, and curious team that knows how to adapt.
Wrapping Up
The message is simple but powerful:
You don’t build resilience by buying more tools—you build it by developing people.
At Blue Cape Security, we help organizations do exactly that—through hands-on, practical training and real-world experience.
Here’s how you can get started:
- Learn, Practice, and Validate — take our on-demand training tracks and build real-world investigation skills through guided labs and scenarios.
- Build Sustainable Capability — contact us for personalized training programs that align with your team’s goals and create measurable, long-term growth.
- Train Together, Live — join our workshops, tabletop exercises, and live cyber range simulations for immersive, team-based experiences.
No matter where you start, the outcome is the same: a stronger, more confident, and capable team—ready to meet today’s challenges and defend against tomorrow’s threats.